Data Security Services Things To Know Before You Get This
and modern technology solutions supply professional support and also service for your network, so you can concentrate on what your organization does finest. The company advantages of handled services in mix with the cash you can conserve make it a wise solution for business of any type of size. is when a business outsources particular IT functions to a third-party service provider, referred to as a Managed Solution Company or.
The goal is to either offer as an IT group for a business that has little or no inner capabilities or to sustain an experienced IT team by taking some of the everyday jobs off their plate. Can managed solutions reduce down cost?
An in-house IT group, on the other hand, includes several more regular and also unexpected costs that can promptly drain your budget plan. Networks featured a great deal of devices that needs to be maintained and in some cases fixed or replaced. upkeep in addition to repairs as part of the agreement, so a solution that might cost you thousands of dollars out of pocket is soaked up by the provider.
Some Known Details About Data Security Services

Getting access to the most effective cybersecurity solutions as well as modern technologies is a crucial asset and also incentive to begin collaborating with a Managed Security Solutions Carrier. A likewise provides independent cyber-security recommendations; this isn't the case for vendors of hardware as well as devices. One of the major benefits of functioning with a Managed Security Solutions Carrier is the broad cyber-security knowledge it supplies, something that numerous firms don't have in-house.
The licensed employees of good MSSPs are constantly familiar with advancements in the sector as well as in modern-day cyber threats. Organizations that place their rely on an are often a lot more reliable at safeguarding their own companies than when they depend on their very own security teams alone. Naturally, this does not alter the truth that both teams need to make correct arrangements about exactly how they communicate with one another.
An MSSP can: Day in, day out, need to manage countless safety and security informs stemming from various safety and security devices used within the company. Basically, notifies usually fall short in their objective: they're either not usable or don't include info that might be utilized to take action. This kind of alert fatigue enhances the chance that real cyber dangers will go unnoticed.
The Best Strategy To Use For Data Security Services
Many cyber-security remedies create combination problems when trading look these up data, causing inefficient and also ineffective data silos. MSSPs typically have actually integrated innovation remedies that fully focus on action-oriented signals. So if your sends you notifies, these are barely ever before redundant or unusable. data security services. A lot of MSSPs make use of the technology of all types as well as dimensions that internal specialists have actually integrated in time for organizations.
And if you need to scale back at a later time, you can. respond quickly. The cost connected with preserving an in-house IT team is a big one, which's why you usually see groups that are understaffed, worn and also incapable to obtain whatever done because of a lack of time and resources.
Training even one additional employee for your IT department expenses countless dollars, as well as there is never an assurance that they'll even remain with the company. An MSP takes in the price of training, as well as you'll never have to stress over your IT experts jumping ship. Scaling networks takes considerable control, manpower and brand-new devices.
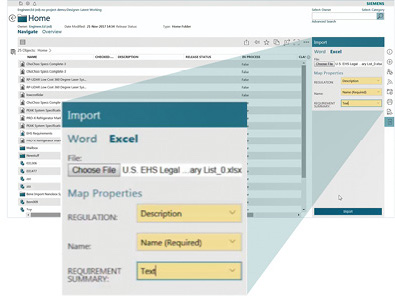
A Digital CIO is a solution some MSPs offer that gives evaluation, method and a step-by-step strategy for the firm's modern technology - data security services.
Data Security Services Can Be Fun For Everyone
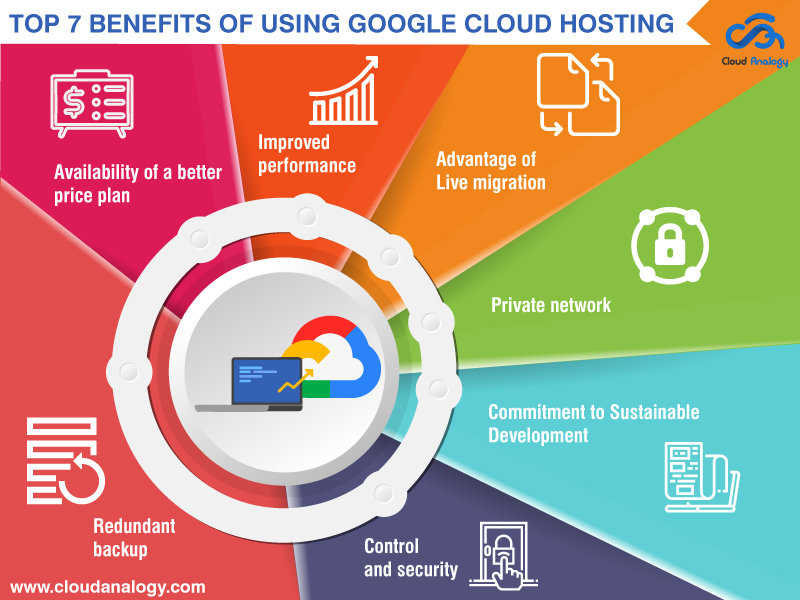
The concept of linking individuals as well as data from anywhere any time look at here cause the development of cloud computing in the 1960s. Yet it occurred with numerous safety threats such as information violation, data loss, hijacking check here of accounts, unconfident APIs, rejection of service as well as expert threats which paved means for the concept of cloud safety.
Catastrophe healing plans can likewise be implemented conveniently when all the details is taken care of in one area. With the right cloud safety and security procedures in position, people can safely access data and applications within the cloud regardless of where they are or what device they use. Cloud computing allows companies to expand greatly, lower modern technology prices and also utilize nimble methods in order to meet the competitors.
As the cloud system is based upon the utility, you have to pay just to the provider just for what you use. Cloud computer enables several individuals to access and also share information while documenting at the same time which makes it very easy for the workers who work offshore or at residence to work on the data quickly and also quickly with any web-enabled solutions.